Network Support After You Trash Your Used Devices

If you’re like most companies today, there comes a time when the devices, desktops and laptops you’re using just don’t offer what the new models can. It becomes important to upgrade so that your staff has access to all the resources and software they need to do their jobs, and so that your company can […]
Improving Router Security | Network Support Tips
A recent article from Alphr makes interesting predictions about the future of computer security. As people come to rely on a wider variety of Internet-enabled devices – not just their laptops or phones, but objects like thermostats, cameras, and sensors – traditional antivirus programs will likely become less important than programs designed to protect routers […]
Questions to Ask When Outsourcing IT Support

Just about every business needs IT support to operate smoothly and efficiently. While some businesses opt to have an entire IT department on site, many choose to outsource IT support to receive the same quality services at a lower cost. If you’re thinking about outsourcing IT support, here are two questions you should ask service providers. […]
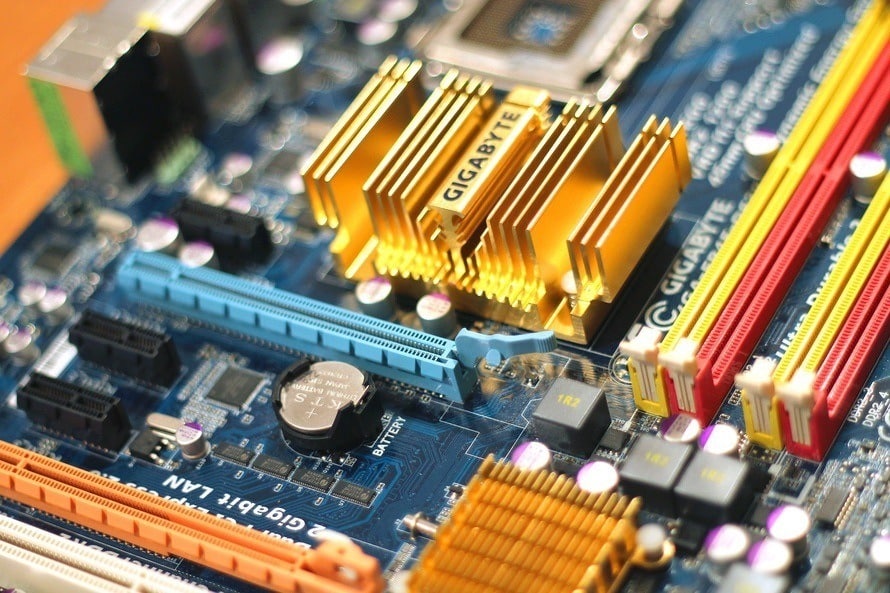
Computer Tip of the Day: Choosing a Brand for Your Small Business

In order to create an effective digital business network for a small company, you must decide on a brand for the office. The computer tip of the day is how to effectively choose a brand that will create an effective network for you. Choosing an OS There is now very little difference between the two major operating […]

