Received a Random Link? DO NOT CLICK ON IT!
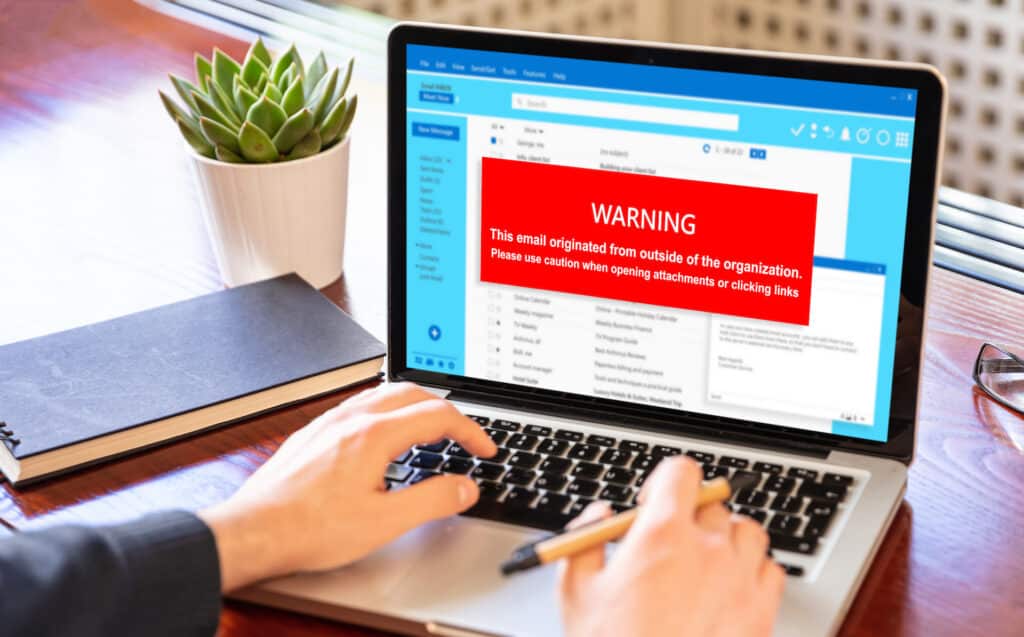
If you ever receive random texts or emails from PayPal (or any other business, for that matter) telling you they suspended your account and now require you to authenticate your identity with an unknown link, then you should definitely think twice before clicking on that link. This is a common method that hackers use to […]
New Malware Affecting Devices Steals Your Money

Many common types of malware can attack your devices to gain information or damage your devices. Android devices now have to keep an eye out for a dangerous malware campaign called “troll fraud malware”. It is signing them up for services and stealing bank details to drain their bank accounts and spend their money. How […]
Ads Can Carry Malicious Code

Sometimes you might be browsing the Internet and come across an advertisement for free downloads of Windows applications. Obviously, this is too good to be true, and hackers tend to exploit advertisements to spread their malicious code across devices. Malvertising is used to deliver various types of threats, all of which can cause considerable harm […]
How Prevent Your Network from Being Sold By Hackers

Believe it or not, your organization’s network can be sold by hackers under the right circumstances. This is the unfortunate reality that we live in. Thus, the commoditization of data and network access has become a real problem. According to a study from KELA, hackers can sell access to compromised networks for a pittance compared […]
3 Cyber Security Issues Businesses Should Prepare For

Cyber security should be a top priority for all businesses, regardless of size. The unfortunate reality is that many business owners do not take the necessary steps to secure their data, which could lead to significant problems further down the line. As technology becomes more advanced and hackers become more sophisticated, it is important to stay […]

