Navigating Cybersecurity Challenges While Working Remotely

When working remotely, you must be vigilant about cybersecurity to protect critical information and prevent cyber threats. Your home office might seem secure, but cybercriminals are adept at exploiting vulnerabilities. Ensuring your remote work setup is secure involves more than just the basics. Stay tuned to discover essential strategies and tools to bolster your defenses […]
Using Encryption to Establish Secure Connections for HIPAA Compliance

For organizations to protect their data, secure connections must be established. To do this, encryption is used as an effective way of ensuring the confidentiality and integrity of data. Encryption works by scrambling plaintext information into unreadable ciphertext, which can only be decrypted with a key for authorized users. This prevents unauthorized individuals from accessing […]
Lessons to Learn in Light of Twitter’s API Breaches

Back in December 2021, an API attack on Twitter took place. It left 5.4 million users with leaked data the following July. The data was put on sale via the black market and was once again put up for sale recently. This shows how disruptive these phishing attacks can be. Today we will discover what […]
Antivirus: Why, Exactly, is it So Important?

Business security is something that both personal and business users need to educate themselves on. It keeps their systems protected from viruses and hackers. Today, let’s take a look at why antivirus is so important and something that we believe every business should put in place this year. What is Antivirus? Any device that you […]
Received a Random Link? DO NOT CLICK ON IT!
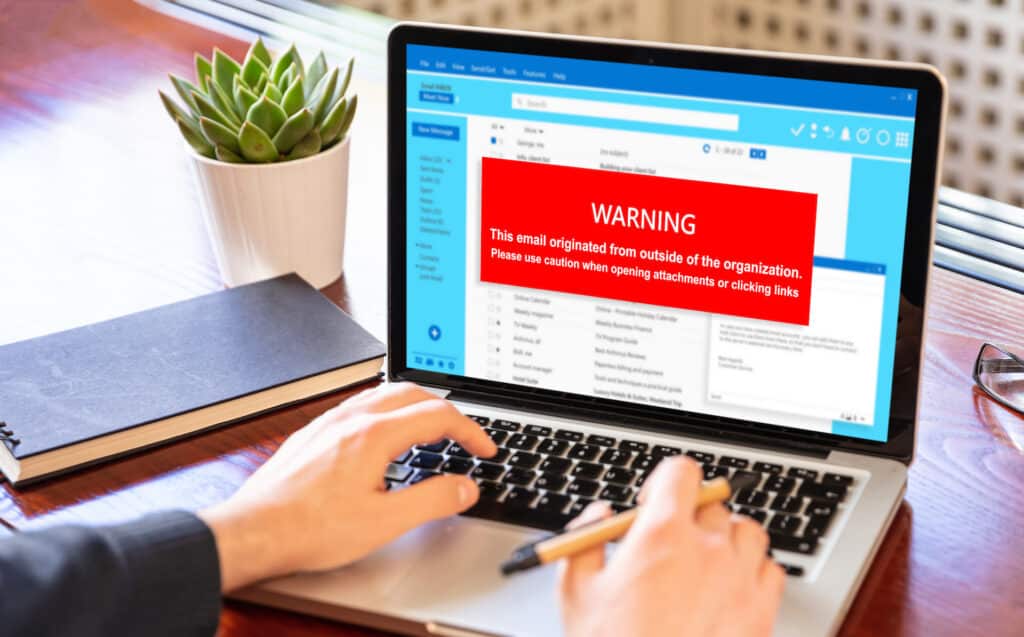
If you ever receive random texts or emails from PayPal (or any other business, for that matter) telling you they suspended your account and now require you to authenticate your identity with an unknown link, then you should definitely think twice before clicking on that link. This is a common method that hackers use to […]

